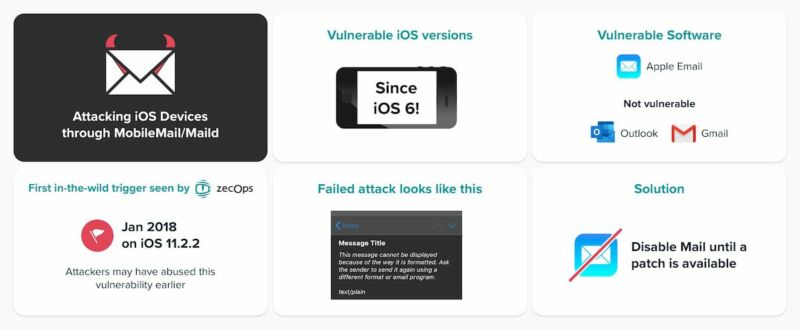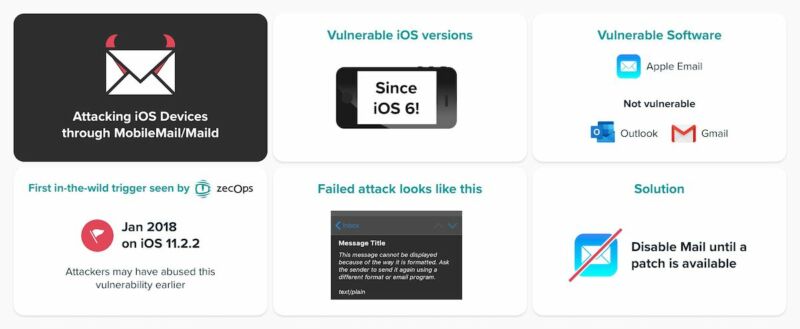
A critical bug that has lurked in iPhones and iPads for eight years appears to be under active attack by sophisticated hackers to hack the devices of high-profile targets, a security firm reported on Wednesday.
The exploit is triggered by sending booby-trapped emails that, in some cases, require no interaction at all and, in other cases, require only that a user open the message, researchers from ZecOps said in a post. The malicious emails allow attackers to run code in the context of the default mail apps, which make it possible to read, modify, or delete messages. The researchers suspect the attackers are combining the zero-day with a separate exploit that gives full control over the device. The vulnerability dates back to iOS 6 released in 2012. Attackers have been exploiting the bug since 2018 and possibly earlier.
Enormous scope
“With very limited data we were able to see that at least six organizations were impacted by this vulnerability— and the full scope of abuse of this vulnerability is enormous,” ZecOps researchers wrote. “We are confident that a patch must be provided for such issues with public triggers ASAP.”
Targets from the six organizations include:
- Individuals from a Fortune 500 organization in North America
- An executive from a carrier in Japan
- A VIP from Germany
- Managed security services providers in Saudi Arabia and Israel
- A journalist in Europe
- Suspected: An executive from a Swiss enterprise
Zerodays, or vulnerabilities that are known to attackers but not the manufacturer or the general public, are rarely exploited in the wild against against users of iPhones and iPads. Some of the only known incidents a 2016 attack that installed spyware on the phone of a dissident in the United Arab Emirates, a WhatsApp exploit in May of last year that was transmitted with a simple phone call, and attacks that Google disclosed last August.
Apple has currently patched the flaw in the beta for iOS 13.4.5. At the time this post went live, a fix in the general release had not yet been released.
Malicious mails that trigger the flaw work by consuming device memory and then exploiting a heap overflow, which is a type of buffer overflow that exploits an allocation flaw in memory reserved for dynamic operations. By filling the heap with junk data, the exploit is able to inject malicious code that then gets executed. The code triggers strings that include 4141…41, which are commonly used by exploit developers. The researchers believe the exploit then deletes the mail.
A protection known as address space layout randomization prevents attackers from knowing the memory location of this code and thus executing in a way that takes control of the device. As a result, the device or application merely crashes. To overcome this security measure, attackers must exploit a separate bug that reveals the hidden memory location.
Little or no sign of attack
The malicious mails need not be prohibitively large. Normal-size emails can consume enough RAM using rich text format documents, multi-part content, or other methods. Other than a temporary device slowdown, targets running iOS 13 aren’t likely to notice any signs that they’re under attack. In the event that the exploit fails on a device running iOS 12, meanwhile, the device will show a message that says “This message has no content.”
ZecOps said the attacks are narrowly targeted but provided only limited clues about the hackers carrying them out or targets who were on the receiving end.
“We believe that these attacks are correlative with at least one nation-state threat operator or a nation-state that purchased the exploit from a third-party researcher in a Proof of Concept (POC) grade and used ‘as-is’ or with minor modifications (hence the 4141..41 strings),” ZecOps researchers wrote. “While ZecOps refrain from attributing these attacks to a specific threat actor, we are aware that at least one ‘hackers-for-hire’ organization is selling exploits using vulnerabilities that leverage email addresses as a main identifier.”
The most visible third-party organization selling advanced smartphone exploits is Israel-based NSO Group, whose iOS and Android exploits over the past year have been found being used against activists, Facebook users, and undisclosed targets. NSO Group has come under sharp criticism for selling its wares in countries with poor human-rights records. In recent months, the company has vowed to serve only organizations with better track records.
It’s generally against security community norms to disclose vulnerabilities without giving manufacturers time to release security patches. ZecOps said it released its research ahead of a general release fix because the zeroday alone isn’t enough to infect phones, the bugs had already been mentioned in the beta release, and the urgency created by the six organizations the firm believes are under active attack
To prevent attacks until Apple releases a general-availability patch, users can either install the beta 13.4.5 or use an alternate email app such as Gmail or Outlook. Apple representatives didn’t respond to an email seeking comment for this post.